Student Technology Guide
(Click on one of the topics below to navigate to that page.)
- Welcome to Eastern
- Your account: NetID and E-number
- PantherMail
- Panther Card
- Passwords
- Safe computing
- Illegal file sharing
- Web privacy
- Computer use policies
- Applications to keep you safe
- Safe Connect on the campus network
- Student computer recommendations
- PAWS
- Wireless network
- Other student technology centers
- Library technology
- Academic technology
- Further help?
Welcome to Eastern
Welcome to Eastern Illinois University. Information technology plays a key role in your educational career at Eastern, and the university strives to provide the appropriate resources and services to enable you to have an exceptional learning experience. This guide provides basic information on the many technological resources available at Eastern our support options section of this guide if you have any technology issues.
Your account: NetID and E-number
Every Eastern student is assigned a technology identity, consisting of a NetID and E-number, as well as a PantherMail email account, when they are first admitted to EIU. Your NetID is a combination of your initials and last name and possibly a number. For example, if your name were Jane Q. Student, your NetID would be jqstudent. Your PantherMail address would be jqstudent@eiu.edu.
If you are a current student, you can confirm your NetID by looking up your name on Eastern’s home page search function (top right of page). Enter your name, then click on “Additional Information” under your name on the Directory Results. Your NetID will be listed at the bottom of the pop-up window.
If you are an incoming student, your NetID and Initial Password can be found at the top of your MyEIU checklist.
Your E-number is your essential means of personal identification at Eastern. To protect against identity theft, the university limits the use of Social Security Numbers, substituting a proprietary nine-digit E-number instead. This number can be found on your Panther Card. Use it to identify yourself in all communication with Campus Technology Support.
PantherMail
Eastern's email system, known as PantherMail, is the official communication channel for all academic and university notices. PantherMail is powered by Microsoft Office 365. You should check your account regularly. Official communication includes class schedules, student financial aid notifications and account statements from the Business Office. Failure to monitor your PantherMail inbox can result in missed messages. It is your responsibility to ensure that your PantherMail account is checked regularly and that it has sufficient free space to receive university communication.
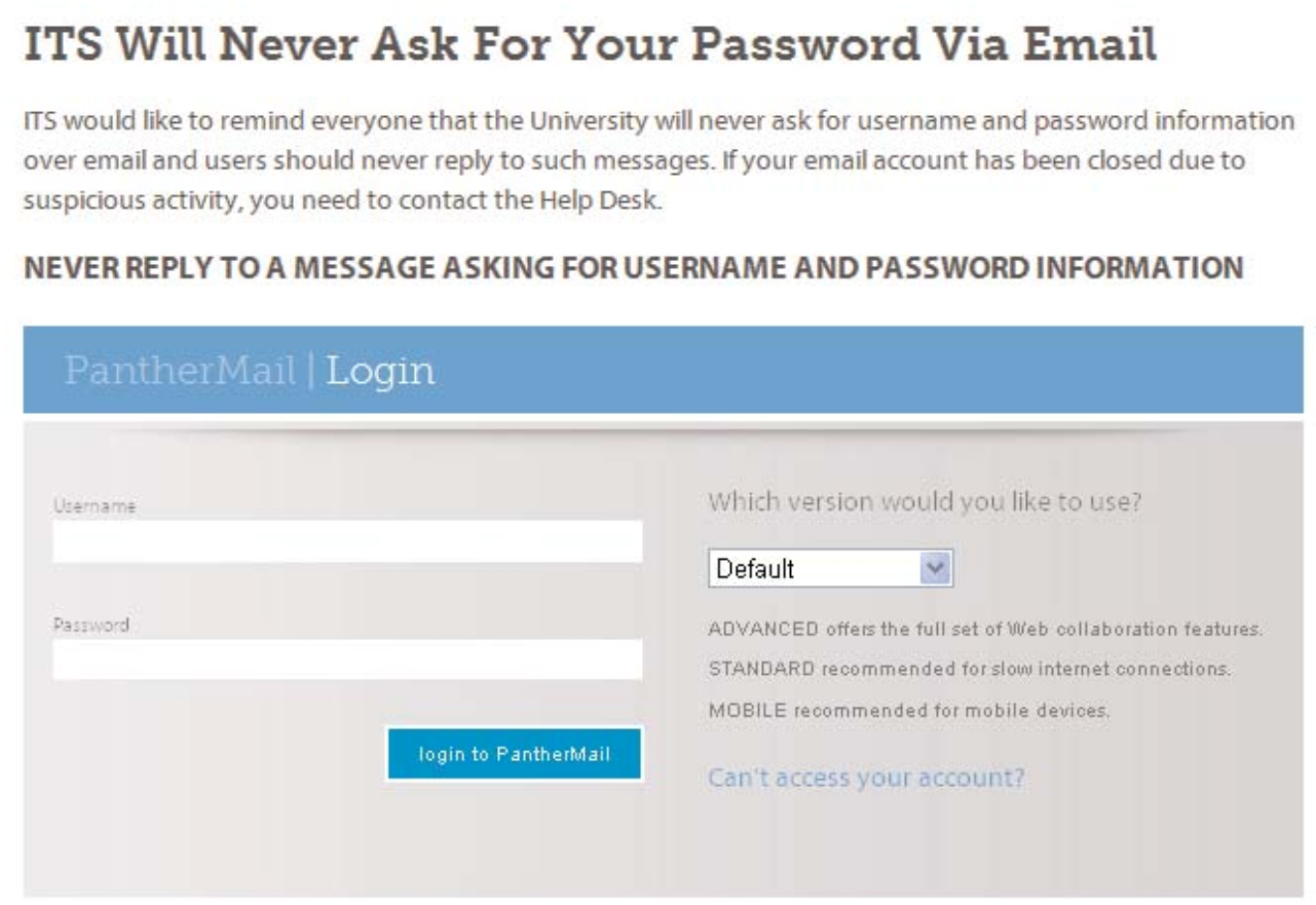
The easiest way to access your PantherMail is via the secure Web interface located at www.eiu.edu/panthermail. All you need is a computer with an Internet connection and a Web browser. No configuration is necessary. Simply enter your NetID and password in the spaces provided in order to get started.
You also can access your account directly from the EIU home page by clicking the PantherMail link in the upper right corner of the page.
You then will see the PantherMail login screen.
Sign in using your EIU NetID as your username and your password. Then click the login button.
You then will see the following screen:
Sign in using your NetID as your username and your password. Then click the login button.
Official university e-mail verification
The university maintains a website that will tell you if an email that you have received was actually sent from Eastern. If you receive an email purporting to be from the university and you are suspicious about its nature, go to our Email Verification page . If the email is listed there, it is safe to open.
Phishing scammers continue to target university email accounts. Be on the lookout for suspicious emails asking for your username and password information. It only takes one or two people to fall victim to a phishing scam to negatively affect the delivery of campus email.
Some quick tips to avoid becoming a phishing victim:
--Never respond to an email asking for password or identity information.
--Never click on a link inside a suspicious email message.
--Check a suspicious email message's URL before clicking on questionable messages to make sure it's not a scam.
--If in doubt, call Campus Technology Support at 581-HELP for advice.
For more about phishing, see the safe computing section of this guide.
Panther Card
Your Panther Card is essential for many of your daily activities on campus. To obtain your Panther Card, visit the Panther Card office, located in Room 3040 of the Student Services Building. Call 581-6596 for information. Your Panther Card is your official university identification card, which you are required to carry with you at all times. Use your card to check out books at Booth Library, gain access to computer labs, utilize printers in those labs, be admitted to the Rec Center, enter sporting events and to attend other university-related functions, purchasing university goods and services, and for on-campus dining.
Your Panther Card is equipped with a smart chip that allows you to carry electronic cash for on-campus purchases. Up to $100 may be stored as Panther Cash on your card. You can add Panther Cash value to your card two different ways. First, add value without cash by coming to the Panther Card office. The value added will be billed on your next month’s student bill. Panther Cash value also can be added to your card in cash increments of $1, $5, $10 or $20 at cash-to-chip machines located across campus. Should your Panther Card be lost or stolen, or your card’s smart chip malfunction, contact the Panther Card office immediately. More information about Panther Card can be found at our Panther Card information website
Passwords
You must create a password to use in conjunction with your NetID to access your EIU accounts. You should choose a password that would be difficult for others to guess, keep it secure and change it occasionally. Never share your password; remember, you are responsible for all activities tied to your account.
When creating a password, choose one that is easy for you to remember but hard for others to solve. Password security, however, does not end with picking a strong password. In order to ensure full password security, you must also take steps to protect your password.
--Never share your password with anyone; it is against university policy to do so. This includes family, friends, significant others, computer support personnel and supervisors.
--Never save your password if prompted by your browser or any other programs.
--Avoid writing your password down.
--Never send your password in email, even if the request looks official. Not only is it against university policy, but such requests are most likely phishing attempts.
Strong password rules:
--The first character of your password must be alphabetic.
--Your password must be a mix of upper and lower case letters.
--Your password must contain at least one number.
--Your password must be at least eight characters long.
--Your password must contain at least one special character from the following list: ! % * - $ :
--Your password may not be longer than 15 characters total.
You should change your password occasionally. To change your password, go to https://password.eiu.edu, where you will see the following screen, and follow the instructions.
To manage your password, sign in with your NetID. Upon initial sign-in, you will be asked to create security questions. After signing in, choose either “Answer security questions” or “use password" to authenticate. You can then proceed to change your password. Follow the on-screen guidelines in creating a new password.
Safe computing
There are a number of steps you can take to help protect your privacy and ensure the safety of your computer.
Phishing attacks
Phishing is an attempt to acquire information such as usernames, passwords and credit card details by masquerading as a trustworthy entity in an electronic communication. If you receive an email asking for personal or account information, do not answer or click on any enclosed links. Remember, Information Technology Services will never ask for your password information in an email. Never answer such requests.
If you receive an email that you feel is a phishing attempt, please forward the email to the following address: phishing@eiu.edu
If your email account has been identified as compromised, ITS will lock your account. Once locked you will not be able to access your email.
To resolve this lockdown, you must call Campus Technology Support at 581-HELP to reset your password and unlock your account.
Protect yourself on social networking sites
Online social sites such as Facebook can provide an easy and fun way to express yourself. However, be careful about how you use those sites. If you follow some simple suggestions, you can minimize the risks to your personal privacy and safety.
--Do not post too much information about yourself. Especially avoid publishing your class schedule, your home phone number and/or cell phone number, your specific whereabouts at any given time, inappropriate photos of yourself or anything else that might embarrass you later.
--Make sure that your profile is set so that it can only be seen by people in your friends list.
--Be wary about adding strangers to your friends list.
--Report any harassment or inappropriate behavior to the proper authorities.
--Remember, Facebook and other social sites can be a source of computer viruses. Download carefully to avoid infecting your computer or the campus network.
Identity theft
Identity theft is one of the fastest growing crimes. However, you can take steps to minimize the risk of becoming a victim.
What is identity theft?
Identity theft happens when a criminal steals a victim's identifying information and uses it to get credit, credit cards, apply for bank loans and even steal money from existing accounts. Most victims find out they have been taken advantage of when they apply for a loan or when creditors call trying to collect on the debts the criminal racks up.
How does identity theft happen?
Identity theft is fairly easy to commit; all that is needed is a Social Security Number, name, birth date and possibly other identifying information such as an address.
Ways to prevent identity theft
--Password-protect sensitive information with non-dictionary passwords and change the passwords frequently (30 days is recommended).
--Shred documents that contain personal information.
--Do not use Social Security Numbers as a form of identification.
--Don't give out your Social Security Number.
--Check your credit regularly.
Lock your computer
If you are going to be away from your computer for a while, make sure it is locked. This will require you to re-enter your password before you can use your computer again. To perform this task on PCs with Windows operating systems:
--On your keyboard, press Ctrl+Alt+Delete at the same time, then click Lock Computer.
--To unlock your computer: Press Ctrl+Alt+Delete again, then type in your password in and click OK.
Reporting a problem
If you suspect that someone has guessed your password and accessed your account, change your password immediately. If you suspect that there is a security breach or flaw in the university system, please notify Campus Technology Support at 581-HELP.
More information about security is available from Eastern's IT security officer, Josh Awalt, 581-1904, or at our Policies page.
Illegal file sharing
Peer-to-peer downloading of music, movies, TV shows, games and other copyrighted material is one of the most problematic Internet activities at Eastern. Illegal file sharing not only is against the law, it also slows your computer and makes it vulnerable to virus infections and spyware and denies network bandwidth to other campus users.
Remember, the Eastern Illinois University network is not to be used to illegally download music, movies, computer programs or any other copyrighted work.
What happens if you download materials without permission?
It is the policy of Eastern Illinois University to respect the intellectual property rights of others (IGP 48.4). If the university is notified that an individual is using Eastern computer equipment and/or network access to download materials without permission, the university will take action to stop such activities.
Any copyright violations traced to students will be referred to the Office of Student Standards for adjudication as a violation of the Student Code of Conduct. Copyright violation penalties may include the loss of network connectivity, community service and monetary fines.
In addition, violations of copyright law can lead to criminal charges and civil penalties. Under current copyright law, criminal cases of copyright violation carry a penalty of up to five (5) years in prison and a $250,000 fine for commercial infringement. Civil penalties for copyright infringement include a minimum fine of $750 for each work. While criminal prosecution for illegal downloading is rare, civil lawsuits are more common.
Common copyright violations at Eastern
The single most common source of copyright violation notices is peer-to-peer programs such as Limewire, BitTorrent, Ares, Frostwire, etc. While these peer-to-peer programs are not illegal in themselves, they can be used in illegal ways. It is important to understand that files shared using these programs may violate copyright law. A good rule to follow is this: If you are downloading something for free that you would normally pay for, there is a good chance that it is illegal.
Information Technology Services has installed new compliance and filtering software which is expected to reduce the level of copyright violations on the campus network caused by students downloading music and video. Eastern utilizes special monitoring equipment to identify illegal file sharing on its network. If this action is identified, students will temporarily lose access to the network with the device identified as conducting the sharing. Notification of this action is performed through webpage messaging. Students will have to confirm to discontinue the activity before connectivity will be restored.
Web privacy
Eastern uses standard Web server access logs and gathers information on the time of day, IP address of the accessing Web browser and destination URL for the purpose of measuring system performance of university-owned computers on the campus network. In compliance with the Illinois State Agency Web Site Act ("Act"), Eastern websites do not use permanent cookies or any other invasive tracking programs that monitor and track website viewing habits. Eastern websites may, however, use transactional cookies (session variables) that facilitate business transactions. While Eastern uses transactional cookies to track your visit to eiu.edu, and our Web server automatically logs the IP/Internet address of your computer, this information does not identify you personally, and you remain anonymous unless you have otherwise provided personal information.
Computer use policies
University computing facilities, equipment, and services are provided for the instructional, research, and administrative computing and information technology needs of the university. University technology resources include, but are not limited to, network and internet access, file storage, computers, email systems, and telephone systems.
Users of university technology resources are expected to utilize good judgment and reasonable care to protect the confidentiality, availability, and integrity of all networks, computers, equipment, data and software owned, leased, or made available by the university.
The university recognizes the following standards of acceptable use and expects each individual in the university community to abide by the following:
--Each individual shall use only those specific technology resources for which they have both authorized access and a need to use. In addition, such use is to be only in the prescribed manner for which the individual is authorized and must be consistent with intended purpose of that specific resource.
--Each individual shall use university technology resources in accordance with all university policies as well as federal, state, and local laws. Each individual shall respect university, departmental, and individual contract and licensing agreements.
--Each individual shall respect the copyright, trademark, and intellectual property rights of others and shall only use copyrighted material in a manner allowed by the copyright.
--Each individual shall respect the personal rights and privacy of other members of the university community.
--Each individual shall refrain from willful damage or destruction of technology resources and refrain from using technology resources to commit harassment, forgery, or fraudulent activities.
Please refer to our Policies for the complete version of the acceptable usage policy.
Applications to keep you safe
- Anti-virus: Installing anti-virus software on your computer will keep it from being infected by computer viruses, worms, adware and spyware. ITS has made a list of anti-virus programs that are compatible with SafeConnect. The list can be found at the Software page
- Software updates: It is very important to keep your computer operating system and other software up-to-date by downloading software patches released by the manufacturer. Software updates often patch potential security breaches which could leave your computer vulnerable to attack. Make sure you are aware of the methods for keeping your software up-to-date.
Safe Connect on the campus network
Network access in the residence halls and on EIU wireless (eiuwifi) utilizes Safe Connect to provide a more secure computing environment for you when connecting to the Eastern network. In order to be allowed access to the network, you will be required to keep your computer's operating system up to date. In addition, Safe Connect will check for the existence of an approved anti-virus program that is running and properly updated.
For complete details about Safe Connect and how to configure your computer, go to our Network and Internet page.
Technical requirements for Safe Connect
-
Which computer operating systems are supported on the network?
Windows 8, Windows 7 (Home Premium, Professional or Ultimate recommended), Windows Vista, Windows XP, MAC OS X, Linux.
-
Which other anti-virus programs are allowed?
A list can be found at our Software page.
-
What else do you need to connect to the Eastern network?
An Ethernet Cable. A Category 6 (Cat6 RJ45) cable will be fastest, but Category 5 (Cat5e RJ45) will allow you to connect. You may bring your own or purchase one at any residence hall front desk.
Remember, if your computer has a Windows or Macintosh operating system, Safe Connect must be installed to access the campus network. Eastern provides students a free copy of Safe Connect.
Installing Safe Connect
All computers in the residence halls and on EIU wireless must have Safe Connect installed in order to be granted full access to network services.
1. Verify that your computer has installed an operational network interface card.
2. Connect one end of your Ethernet cable into the network interface card and the other end directly into the orange data jack on the wall (if using desktop computer in residence hall room.)
3. Turn on your computer and open up a Web browser. You will see the “Welcome to the Campus Network” login screen.
4. Enter your NetID and password (the same one you use for PAWS and email access).
5. After you read the policy and indicate that you understand it, close out that window and click “Yes, I Will Install the Policy Key,” and accept the terms and conditions for Internet use. If you select “I Do Not Accept,” you will see a popup window acknowledging your decision telling you that you have been declined access to the network.
6. Safe Connect will do an initial policy check to verify your software, patches and antivirus compliance. This check should take less than 30 seconds. You will then see the following screen:
7. If your machine does not pass the validation rules, you will be redirected (below) to pages that will help bring your machine into compliance.
8. Once you have complied with all of the validation rules, you will be successfully connected to the network.
Issues users may have with connecting to the network:
- Windows is not up to date: Keeping your Windows operating system up to date will ensure that your computer has all the latest security enhancements necessary for a more secure computing experience. Microsoft typically publishes updates on the second Tuesday of each month. It is a good idea to ensure that your computer is set to automatically check for updates on a regular basis.
- Anti-virus definitions are not up to date: Anti-virus software is required to be kept up to date with the most current protection against viruses. If the Safe Connect system detects that your anti-virus software is out of date, you will be required to update it before accessing the network.
- Malware is interfering: If you have problems with your machine, it could be due to malware (otherwise known as spyware or adware) being present. Be sure to run your antispyware programs. These programs can help to remove potentially harmful programs and not only help your computer run properly but also improve the performance of your computer. See our Software page.
Apple anti-virus requirements
A list of anti-virus programs can be found at our Software page.
Safe Connect Broadcast Messaging
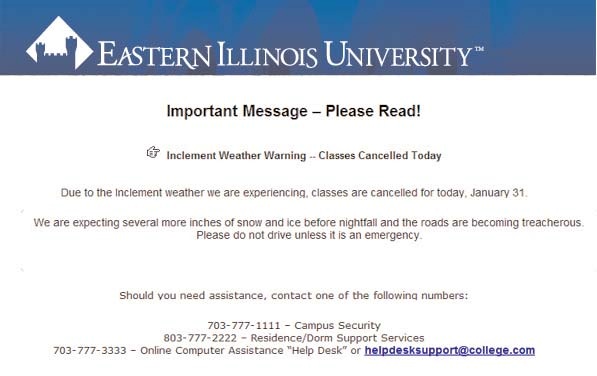
A unique feature of Safe Connect is its ability to provide notification of emergency situations such as class cancellations or severe weather warnings. This feature delivers real time on-demand informational messaging automatically, flashing a window such as the one seen following, on your computer screen.
Student computer recommendations
Eastern does not require most students to bring their own computer to campus, although some academic programs do require specific kinds of laptops. While Eastern offers access to computers via several labs located across campus, many students find that owning a computer is more convenient and enhances their academic experience.
Most modern computers, laptops, tablets or mobile devices will work on our network. Below are guidelines to help in purchasing a device to bring to campus.
Hardware
To ensure a better experience with the Eastern network, we recommend the following, regardless of which operating system you are using:
- Memory (RAM): 2GB minimum
- Wireless Card: 802.11 b/g/n
- Ethernet Card: 10/100 capable
Operating system
Our wireless network uses management software called SafeConnect. This helps to ensure our student computers are meeting some recommended standards to prevent campuswide virus outbreaks. SafeConnect supports the following Operating Systems:
- Windows Vista (supported, but not recommended)
- Windows 7
- Windows 8
- Mac OS X 10.9 to 10.12
Any beta versions of operating systems are not supported. As operating systems are updated, SafeConnect is updated to support them. Occasionally, there will be a delay between operating system updates and SafeConnect Support.
Antivirus software
ITS requires all computers, Windows and Mac, to be running an up-to-date Antivirus software.
The following antivirus software is free for personal use from other providers:
- Avast Antivirus
- Microsoft Security Essentials
- Sophos Antivirus
Internet browsers
We recommend having at least two Web browsers installed on your computer. Occasionally, some Web service providers do not offer the best experience between each browser. If you are using one browser and run into an issue, we suggest trying a different browser first, as a troubleshooting tip. Most Eastern Web-based services support using the most current versions of the following browsers:
- Internet Explorer
- Firefox
- Chrome
- Safari
Additional software
Many courses require students to write papers, create spreadsheets, update websites, and more. You can find some additional recommended software, available for personal use at our Software Download page here.
As a precaution, please check with your college or course professor for any additional software that may be required.
Printers
There are many printers in labs on campus where students have access to print, for a fee. Some can even be printed to from your residence hall. However, if you choose to bring your own printer to campus, be aware that Eastern's wireless and residence hall network does not support personal printers. If you bring your own printer, be sure that it can be plugged into your desktop or laptop via USB or other compatible printer cable.
Mobile devices
Eastern's wireless network is capable of recognizing a variety of mobile devices and their corresponding operating system. Use the information below to help ensure your mobile device will work on Eastern's wireless.
Mobile phones and smaller handheld devices
- iPhone
- iPod touch
- Android phones (most of them)
- Galaxy Note
- Windows Phone 7
- Windows Phone 8
Tablet devices
- iPad
- Galaxy Tab
- Kindle Fire
- Nook Color
- Surface RT
- Surface Pro
- Chrome OS devices
Laptop Information
Presently, some departments on campus require the use of laptops in classrooms. Please contact your individual class program to learn about any requirements or recommendations your program may have:
- Art: https://www.eiu.edu/art/
- Journalism: https://www.eiu.edu/journalism/
- Communication Studies: https://www.eiu.edu/commstudies/
For students who prefer to purchase a laptop computer, Eastern makes recommendations
for minimum specifications. These can be found at the User Services Web page, here at Self Help, and will be academically appropriate and compatible with the EIU network. Major computer manufacturers offer special educational promotions to Eastern students. Links to these discounted offers are available from this website and at the EIU Union Bookstore.
How to use the program
Eastern has established relationships with computer manufacturers to offer laptop computers to the students and their families at an educational discount. The manufacturers have established sites for EIU students to purchase a laptop configured to meet the recommended minimum specifications to be compatible with the ElU networks. The customer service representative of the manufacturer will answer any question you may have about the configurations.
A particular academic major may have specific requirements for a laptop configuration. It is recommended the student visit the website of the academic department to determine if the department has different requirements. The academic departments’ website can be located at the EIU "A to Z Index" and information about laptop requirements is available at the EIU Union Bookstore.
Eastern recommends the student purchase warranty service and accidental damage protection for as long as the student will own the laptop. Additional accidental damage protection and coverage for loss may be covered by the family homeowners insurance. Eastern is not responsible for service of the laptops; students will need to follow the manufacturer's instructions for service.
Students who have not reached their annual academic year maximum for a Federal Direct Student Loan may be considered for a loan increase to assist in funding the purchase of a personal computer. Contact the Office of Financial Aid at finaid@www.eiu.edu or call 217- 581-3714.
Frequently asked questions
What happens if I have hardware problems with a non-program laptop?
Hardware warranty service on computers that are not in the program may not be available without a charge. You must follow the instructions for that manufacturer's warranty. For example, if your hard drive fails, you may have to ship the computer back and be without it for a week or longer. The company may send you the part and require you to replace it yourself.
What if I spill something on my computer or accidentally damage it?
Warranty service and accidental damage protection may be purchased from the manufacturer at the time of purchase. Eastern recommends the student purchase warranty service and accidental damage protection for as long as the student will own the laptop. Additional accidental damage protection and coverage for loss may be covered by family homeowners insurance. Eastern Illinois University is not responsible for service of the laptops; students will need to follow the manufacturer's instructions for service.
If my non-program computer crashes, will it be restored back to use?
The operating system and other applications can be restored for an hourly charge. For an EIU Student Program Laptop, the hard drive will be restored to its original imaged state including MS Office, if it was purchased. All anti-virus and other operating system software will be restored at the service center.
Can I buy the support package without the entire Laptop Program?
No. The Eastern Illinois University Laptop Program is a bundled value only available on the standard models chosen by the university.
What's the difference between a consumer-class and business-class laptop?
Consumer-class laptops are designed for the single home user for entertainment and daily tasks and generally include only a one-year warranty with limited technical support requiring you to send the laptop to the manufacturer for repairs. Business-class systems are built around security, reliability, manageability and affordability with much longer, stable lifecycles. With EIU's Laptop Program, you will be receiving only the highest quality business class laptop available with on-campus technical support and service.
The Student Laptop Program includes: Top-of-the-line laptops configured to meet or exceed Eastern Illinois University minimum technical standards. On-campus support: Hardware support at EIU Union Bookstore Service Center, three- four-year accidental damage protection available, loaners and Help Desk support. Norton Antivirus and anti-spyware software required by Eastern pre-loaded onto your laptop.
PAWS
PAWS (Panther Access to Web Services) enables students to access their personal information via the Internet. All you need is a computer with access to the Internet and a Web browser. Through PAWS, students can securely:
- Register for classes
- Look at student payroll records
- Pay university bills
- View the course catalog and class schedule
- Access financial aid
- See records and transcripts
- Obtain a parking pass
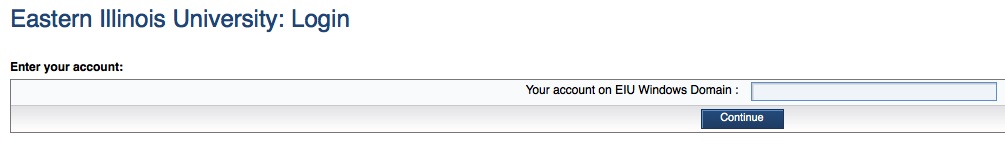
To access PAWS, click the “PAWS” link at the top right corner of the EIU homepage.
You will then see this screen:
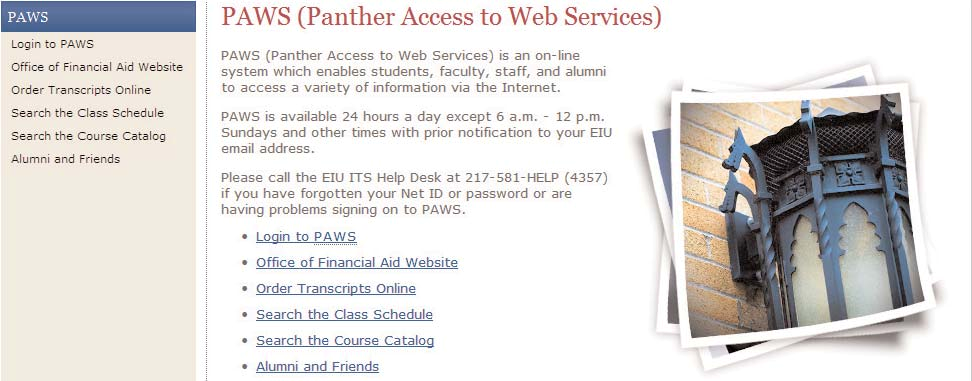
Click the “Login to PAWS” link.
You then will see the following screen:
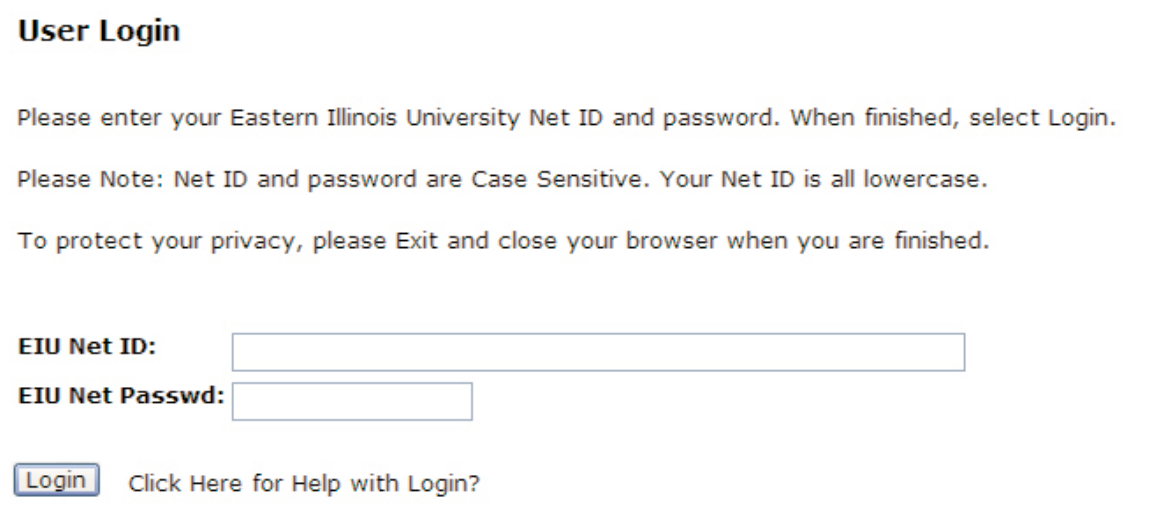
Login to PAWS using your NetID and password.
Wireless network
Using the wireless network
The wireless network at Eastern enables laptop computers, tablets and smartphones to connect to the campus network rather than via traditional Ethernet cable, allowing greater mobility and connectivity. Information Technology Services has provided wireless access points throughout every academic building and most residence halls on campus.
In order to utilize wireless, when purchasing a laptop or table computer, make sure you buy one with an internal wireless card meeting 802.11g or n specifications. If your notebook does not have a wireless card, you will need to purchase one in order to connect to Eastern’s wireless network.
Caution: Wireless not encrypted
Wireless Internet access at Eastern is neither secure nor encrypted. Use of the wireless network for anything other than general Web browsing is not recommended. You should never send sensitive data such as Social Security Numbers or financial information over the wireless network.
Wireless availability on campus
All administrative, academic areas and residence halls on campus are covered by a wireless signal. Coverage tends to exceed these boundaries. Your reception may vary by location and network traffic loads:
No private networks
Students living in residence halls are not permitted to install routers on the campus network in order to create their own local area network. Private routers can interfere with other network traffic, even potentially causing network outages, and are prohibited by university governing policies.
Other student technology centers
Cyberlounge
The Cyberlounge is located in the Seventh Street Underground in the University Union. It is a quiet, relaxing atmosphere for studying, watching television or writing papers. The lounge includes a number of desktop computers available for student use. Hours are:
- Monday-Thursday 7 a.m.-11 p.m.
- Friday 7 a.m.-1 a.m.
- Saturday 10 a.m.-1 a.m.
- Sunday 11 a.m.-11 p.m.
Library technology
Computer workstations
Booth Library has more than 170 computers located throughout the building available for student use. Forty-eight of these computers, located near the Reference Desk, are designated for research in the Library’s databases and online resources. The remaining computers are available for general use and offer applications for both Mac OS and Windows 8. A list of software available in the library is available at http://www.library.eiu.edu/lts/software.pdf
Computers do not require a reservation or login and are available on a first-come, first-served basis. The main computer lab has 58 computers and is located on the 4000 level just past the Library Technology Services counter. Also on the 4000 level is the e-classroom with 25 computers. This classroom is used for training, workshops, and presentations but is open as a public lab when it is not scheduled for instructional use. Two group study rooms on the 4000 Level are equipped with collaboration monitors. Laptop computers can be connected to these large monitors to facilitate group collaboration and discussion. Additional public computers are available on the east side of the 1000, 2000, and 3000 levels.
Media Lab, located behind the Library Technology Services desk, is equipped with scanners, 27 inch monitors, and an audio digitization station for cassettes and LPs. Specialty software installed in Media Lab+ includes Mathematica, Mathlab, and Anaconda. Screen reader, screen magnifier, and mind-mapping software is also available on certain Media Lab stations.
For questions about computing resources in Booth Library, call (217) 581-6091.
Additional Equipment
Three Apple SuperDrives are available for checkout at the Library Technology Services counter for use with computers that do not have an internal CD-ROM drive. Headphones, micro USB cables, SD card readers, calculators, microphone headsets and cassette tape player/recorders are also available for checkout. Two Blu-Ray players and four electric typewriters are provided for use inside the library.
Other Services
The library can laminate legal or letter size items for 50 cents per page. Transparency printing is available at 50 cents per page.
Networks
All study tables in the building offer standard Ethernet jacks. Ethernet cables are available for checkout at the Library Technology Services counter. Wireless Internet access is available throughout the building for anyone with a wireless enabled device such as a laptop, tablet, or smartphone.
Printing and Web-based printing
At the library, printing costs are applied to your EIU student account by swiping your Panther Card at a print station in the lab on the 4000 Level. Printing is 8 cents per page for black and white and 16 cents per page for color. If you do not have your Panther Card with you, a library print card may be purchased for a dollar, which will provide 10 black and white or five color prints.
Web-based printing is available for Booth Library users to send print jobs from a laptop or other device to print stations on the 4000 Level. Simply create a document using your own computer with Microsoft Word or Adobe Acrobat PDF. Then, submit the print job over the Internet and come to the lab on the 4000 Level within 24 hours to print your document. Complete instructions are available at http://print.eiu.edu. Remember to bring your Panther Card when you come to the lab to print your documents. If you have questions about Internet printing, contact Library Technology Services at (217) 581-6091 or visit their service desk on the 4000 level of Booth Library.
Off-campus users
All of the catalogs, databases, and other electronic resources linked to Booth Library’s website are available for use off of the EIU campus. You will be prompted to enter your EIU NetID and password for access to some resources from off campus.
Contacts
- Reference librarians: 217-581-6072
- Ask A Librarian: www.library.eiu.edu/requests/asklibr.html
- Library Technology Services: 217-581-6091
- Circulation Services: 217-581-6071
- Office of the Dean: 217-581-6061
For a complete list of hours, check the Booth Library Web site at:
www.library.eiu.edu/about/hours.html or call the Hours Hotline at 217-581-6423.
Fall and Spring Sessions
- Monday - Thursday, 8 a.m. to Midnight
- Friday, 8 a.m. to 5 p.m.
- Saturday, 9 a.m. to 5 p.m.
- Sunday, noon to Midnight
Intersession:
- Monday - Thursday, 8 a.m. to 10 p.m.
- Friday, 8 a.m. to 5 p.m.
- Saturday, 9 a.m. to 5 p.m.
Summer Session:
- Monday - Thursday, 8 a.m. to 10 p.m.
- Friday, 8 a.m. to 5 p.m.
- Saturday, 9 a.m. to 5 p.m.
- Sunday, 2 p.m. to 10 p.m.
Academic technology
The Center for Academic Technology Support (CATS), is a campus resource center for a variety of services and technological solutions. CATS is committed to supporting and promoting all academic departments in the use of information and communication technologies for teaching and learning at Eastern Illinois University. CATS services include technology training, digital & multimedia, mobile & web applications, online course development, and the Gregg Technology Center (GTC).
ATAC
The Academic Technology Advisory Committee (ATAC) provides a university-wide forum for discussion of technology issues and the development of recommendations for strategic direction concerning the use of academic communication, computation, information and instructional technologies. The funding, which is provided by students via the Computer Technology Fee, is dispersed by ATAC to provide technology enhanced classrooms and computer labs in order to enhance the learning of students attending Eastern.
Technology-Enhanced Classrooms
Eastern has 205 Technology-Enhanced Classrooms (TECs) with a variety of equipment configurations and seating capacities. These rooms create new opportunities in teaching and learning by integrating computer, multimedia and network technology. Each classroom includes a wall screen, video projector, CD/DVD player, audio system and computer with a high-speed Internet connection. Many TECs also have document cameras, Starboards and Smart Boards.
ATAC Labs
There are three general-use labs located across the Eastern campus. These labs are available for use by all Eastern students. All labs are staffed with student lab consultants who are available to provide users with computing and printing assistance. Lab locations are:
| Lab Name | Location |
| Gregg | Gregg Technology Center (GTC, directly west of Booth Library) |
| Booth Lab | Booth Library 4000 Level |
| Lumpkin Lab | Lumpkin Hall 1020 |
Discipline-aligned labs
Discipline-aligned labs implement software designed for specific use by academic area. Frequently, the hardware and software found in a discipline-aligned lab meets specific requirements of an academic program.
| Lab Name | Location |
| Biological Science Lab | Life Sciences 1130 |
| Communications Studies | Coleman Hall 1781 |
| Computer Integrated Manufacturing | Klehm Hall 3135 |
| English | Coleman Hall 3120 and 3210 |
| Foreign Language | Coleman Hall 1150 |
| Journalism | Buzzard Hall 2434 and 2436 |
| Lumpkin | Lumpkin Hall 1011, 1021 and 1120 |
Gregg Technology Center (GTC)
The GTC is one of three open labs on campus. The open computer lab area consists of 19 dual-boot iMacs which are available on a first come-first serve basis. An additional 25 computers are made available when the Training Classroom is not in use. Printing services are available through two black and white and one color printer via the Uniprint system. Printing requires the use of a Panther Card from which printing costs are deducted from the smart chip.
Other areas and services of the GTC include:
GTC equipment checkout
Equipment available for checkout at the GTC includes - digital cameras, video cameras and accessories, card readers, headphones, cables, webcams, and laptops. Note some items are for in lab use only.
Visit our Instructional Services page to reference documents pertaining to policies and checkout length. All equipment checkouts require the EIU Panther card.
GTC Training Classroom
The Gregg Technology Center has the capability of converting part of its space into a multimedia classroom. This training area consists of 25 dual boot iMacs, video projection, Starboard, self-projecting Smart Board, and access to Wi-Fi technology.
Training services for students
Student Technology Training is a service of CATS located in the Gregg Technology Center (GTC). It provides EIU students technology demonstrations, training, references, and support that advocates a total integrated learning experience by enhancing technology skills used to complete coursework, conduct research, complete service learning activities, and achieve personal development. Training sessions are offered each semester in the GTC training classroom and in-class by instructor request. A semester schedule of training session topics, dates, and times are available at www.eiu.edu/cats. A collection of technology resources is also continuously updated on the same website. For more information, contact CATS D2L Assistance (217)-581-8452
GTC Multimedia Area
Equipped with an array of AV equipment, soundproof booth, and Mac Pro editing stations, the GTC Multimedia Center provides students the ability to produce videos start to finish. **
The Multimedia Area consists of six Mac Pro tower stations each loaded with iMovie, Adobe CS (Adobe Premiere, Soundbooth, Photoshop, etc.), and Final Cut software in order to create or edit a plethora of multimedia. In addition to the aforementioned software, miniDV/DVD decks; professional-grade scanners; webcams; Snowflake microphones; aWACOM Intuos graphic tablet; all are available for use upon reserving one of the stations. Attached to the Multimedia Area is a conference room which students and staff may reserve for practicing classroom presentations, training sessions, meetings, or even video conferences. Located behind the GTC Checkout Area, a soundproof booth provides an environment in which an iMac computer equipped with an iSight camera and microphone can be used to record voice, computer screen, and/or computer camera visuals. As it is for all checkout items, in order to use the booth you must have your Panther card.
**Upon request, manuals are available for instruction on how to use all the equipment in this area, and the Gregg Technology Center staff is available for assistance as well.
Collaborative Areas
The Gregg Technology Center has four collaborative areas for students working in groups for class projects. There are four collaborative dual boot iMac stations and one larger collaborative area with videoconferencing and a dual-boot iMac.
The Multimedia Center
The multimedia area in the Gregg Technology Center has been set up for students to use when making classroom presentations or working on classroom projects. There are three dual boot iMac stations. Each station contains video editing software, which can be used for producing digital video presentations, authoring your own DVDs or converting older media such as VHS tapes to DVD.
The computers in this area are also equipped with 8mm digital film recorders/players, VHS recorders/players, Web cams, professional scanners and LCD television monitors. A graphics-drawing tablet also is available.
Students needing to convert an older analog video source into digital media may do so with a digital non-linear accelerator.
Manuals are available for instruction on how to use all the equipment in this area, and the Gregg Technology Center staff is available for assistance as well.
Assistive Technology Stations
There are three dual-boot iMacs in the Gregg Technology Center which are ADA-compliant stations for students with specialized needs. These workstations utilize specialized software such as JAWS, Win Braille, Kurzweil, both Microsoft and Apple accessibility software for those students with text-based disabilities, low vision, auditory learners, English as a second language learners, and any other students who prefer hearing text spoken rather than reading a screen. In addition, students using this area also have access to a Braille printer.
For more questions about aforementioned needs, the Office of Disability Services is located in Ninth Street Hall. If you have any questions regarding assistive technologies, contact the Office of Disability Services at 581-6583.
Blackboard Collaborate
Blackboard Collaborate (formerly Elluminate) is a Web-based video conferencing system which allows participants to engage in two-way audio, multi-point video, interactive whiteboard, application and desktop sharing, rich media, breakout rooms, and session recording. Some faculty use Collaborate to connect with students online. Online Rooms in D2L are conducted using Blackboard Collaborate. More information can be found at https://www.eiu.edu/collaborate
D2L ePortfolio
ePortfolio is an online space in D2L where students can keep and manage a digital collection of your personal and academic resources. Go to https://www.eiu.edu/d2leportfolio for more information.
EIU Online - Desire2Learn
EIU Online is powered by Desire2Learn (D2L). D2L is the official learning management system for all courses at EIU. D2L provides a virtual learning environment for faculty to deliver and extend classroom instruction to students. D2L is used to deliver complete instruction in online classes, as well as supplement traditional classes that meet face-to-face.
To access EIU Online:
1. Go to: www.eiu.edu
2. Click on "d2l" in the upper right corner
3. Type in your NetID, (i.e. first part of your EIU email address minus @eiu.edu) and password.
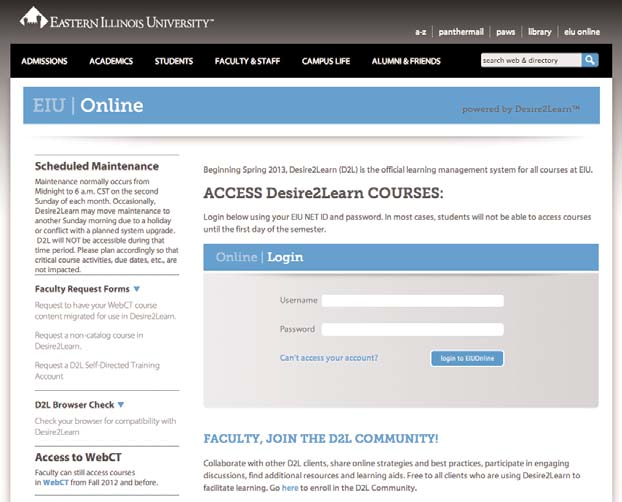
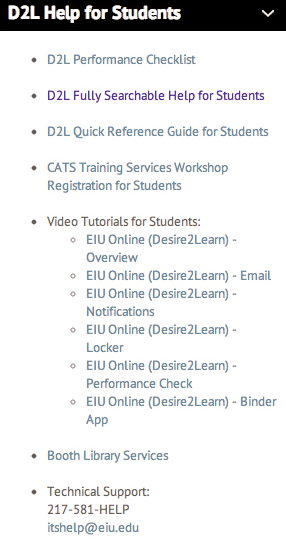
4. Once logged in, D2L resources for students can be located in the "D2L Help for Students" widget (see picture below). This widget is continually updated with video tutorials, pdfs, links, etc. that explains to students how to best use and navigate D2L. For additional assistance using D2L, students may contact Center for Academic Technology Support (CATS) D2L Assistance at (217)-581-8452
Qualtrics
Qualtrics enables students to conduct online data collection and analysis including market research, customer satisfaction and loyalty, product and concept testing, employee evaluations and website feedback. Go to https://www.eiu.edu/qualtrics/ for more information.
Respondus LockDown Browser (RLDB)
Respondus LockDown Browser is a custom browser that locks down the testing environment within EIU Online. When students use Respondus LockDown Browser they are unable to print, copy, go to another URL, or access other applications. RLDP is a free download to students. If an instructor requires the use of RLDB for a quiz, the student will be prompted to download and install the software before beginning the quiz.
Turning Point
Turning Point is a student response system (clickers) used within some classrooms. Information regarding Turning Point can be found at https://www.eiu.edu/turningpoint
Turnitin
Turnitin is a tool for both faculty and students to enhance the writing process. Created from the collective efforts of researchers, teachers, mathematicians and computer scientists at UC Berkeley, the Turnitin program has helped with the detection of improperly cited written works using an Internet-based electronic service.
This tool assists both undergraduate and graduate students in creating authentic and original written works. The tool also helps educators instruct students how to properly cite and reference resources used in the creation of their written works.
Eastern Illinois University acknowledges the use of Turnitin as a learning and evaluation tool. The goal is to provide students with the necessary skills and knowledge to successfully and properly cite references while composing original and authentic written works for classes and professional publications.
For further information about Turnitin, go to http://castle.eiu.edu/turnitin/student.php
Web Office
The Web Office is here to assist you with all your Web-related needs. Services are extended to all campus departments, faculty members and student organizations. Following are some examples of the Web Office’s extensive services:
- Creating a new website.
- Updating an existing website.
- Setting up advertisement of an event on eiu.edu.
- Managing the EIU online calendar.
- Web development -- surveys, forms, etc.
- Email newsletters.
- Assistance writing/editing Web content.
Need further help? Here’s where to get it:
Located on the Second Floor of the Student Services Building (the red brick building located between Old Main and the Martin Luther King Jr. Student Union) in Room 3040 (The PantherCard Office), can give you live, local assistance with all of your technology questions.
- You can contact Campus Technology Support by phone by calling 581-HELP (4357).
- You also can get assistance in person. Walk-ins are welcome, and staff members can answer how-to and troubleshooting questions on a variety of computer and connectivity related issues and assist you with password and software problems, as well.
- In addition, you can email your technology questions to itshelp@eiu.edu.
- If you live in a residence hall, you may call the Housing Help Desk at 581-7708 for support.
- For issues pertaining to campus network access from the residence halls, students may bring their computer to the support center in Taylor Hall for assistance.
ITS Help Desk Support Requests
Create a request for support online by filling out this: Tech Support Request Form
Live Chat
ITS Help Desk Live Chat connects you with an ITS technician in real time. Live Chat is available Monday-Friday, 9 a.m. to 4 p.m. during summer hours: Live Chat
Follow User Services’ Twitter feed to keep current on service outage announcements and other information: @PantherTechHelp.